
Firewall protects your infrastructure from simple external attacks, from viruses contained in emails and websites as well as malware. A well designed system also protects your company against phishing attacks.
Explore the offer
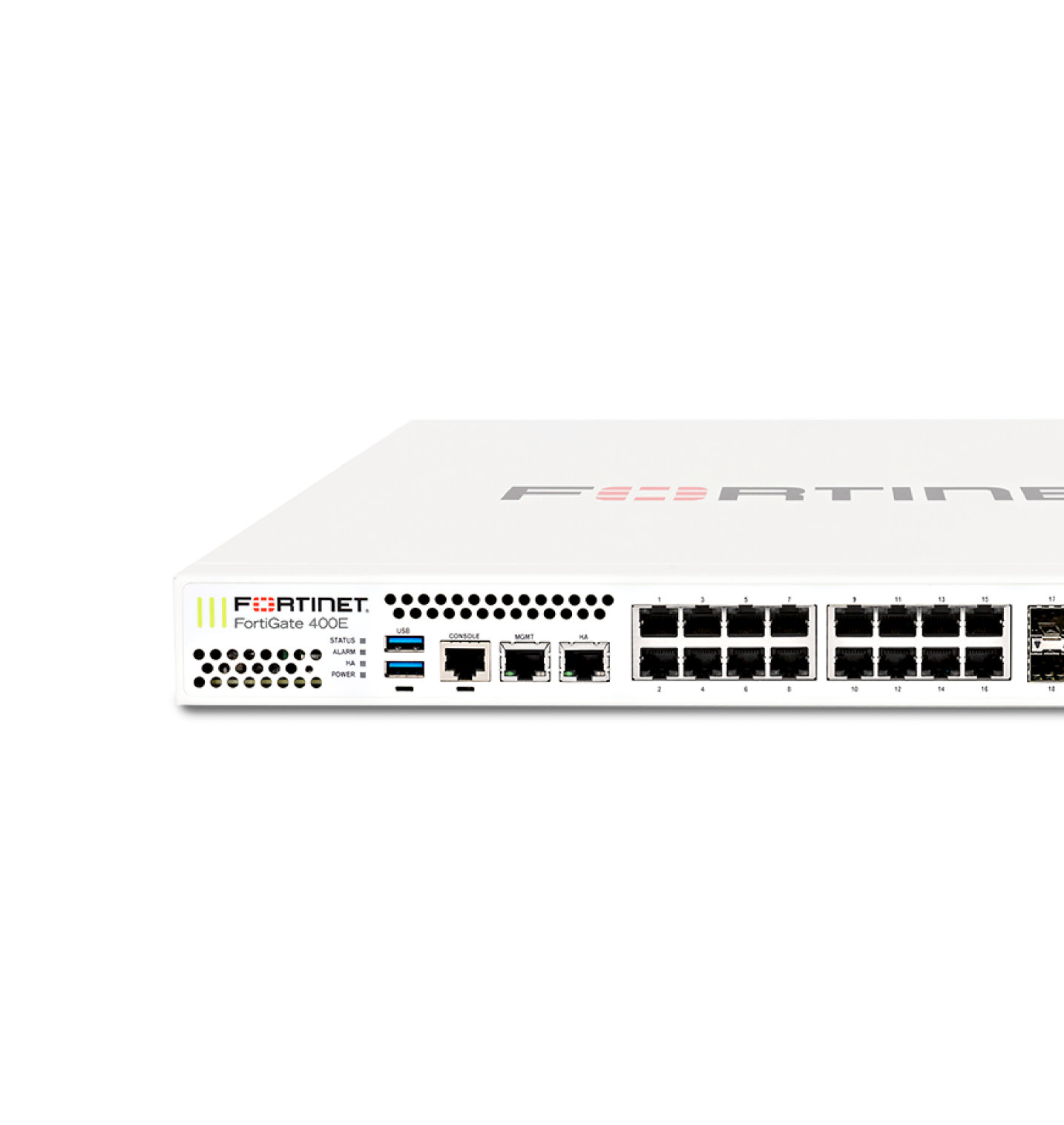
At ITH, as part of our Network as a Service package, we offer access to state-of-the-art Fortigate firewalls, which we supply for you along with full 24x7 service and support.
What do you obtain as part of the service?
| Fortigate 40F | Fortigate 60F | Fortigate 100F | Fortigate ITH Cloud | |
|---|---|---|---|---|
| Recommended for the link | 500Mbps > | 1Gbps > | 10Gbps < | 1Gbps > |
| Monitoring by ITH NOC | ||||
| Management by ITH NOC | ||||
| Customer self-administration possible | ||||
| SLA |
Standard Various packages available |
Standard Various packages available |
Standard Various packages available |
Standard Various packages available |
| IPS throughput | 1Gbps | 1.4Gbps | 2.6Gbps | 900Mbps |
| NGFW throughput | 800Mbps | 1Gbps | 1.6Gbps | 700Mbps |
| Threat Protection throughput | 600Mbps | 700Mbps | 1Gbps | 400Mbps |
| Number of Client-to-Gateway IPsec VPN tunnels | 250 | 500 | 16000 | No tunnels |
| Throughput for SSL-VPN | 490Mbps | 900Mbps | 1Gbps | 1.5Gbps |
| Number of SSL-VPN user sessions (simultaneous sessions) | 200 | 200 | 500 | No sessions |
| SSL Inspection throughput | 310Mbps | 630Mbps | 1Gbps | 500Mbps |
| Full technical specifications from the manufacturer | ||||
| Activation fee | 500 PLN | 500 PLN | 1500 PLN | 600 PLN |
| Monthly subscription |
280 PLN / month | 380 PLN / month |
1500 PLN / month |
600 PLN / month |
| Order | Order | Order | ||

Are the above parameters not sufficient for you?
No problem - we also offer higher-end units than the Fortigate 100F, please contact us so that we can prepare an individual quotation.

A dedicated UTM/Firewall solution applied to the corporate network protects it also from within. Very often, the weak links in an infrastructure are the devices that are connected to the network, which are not very configurable, such as printers, IP cameras and other devices that are most often associated with the so-called "Internet of Things". Our proposed 24x7 solution analyses network traffic and, if any anomalies are detected in network traffic, immediately blocks it and reports back to the ITH engineering team.
 ● Attacks through an IP printer
● Attacks through an IP printer ● Attacks through IP cameras
● Attacks through IP cameras ● Unauthorised access by unauthorised devices
● Unauthorised access by unauthorised devicesThe system also makes it possible to block employees from accessing selected sites or content, e.g. pornographic sites, social networking sites, etc.

A provider-side virtual firewall is an innovative solution that requires little investment from the user.
For company use, a virtual firewall solution or a dedicated instance on a large firewall device that is installed in the ITH Data Center is provided.
● The system is redundant
● Full management on the part of ITH
● User can modify his/her own security rules and policies in the Subscriber Panel
● No capital expenditure on the part of the customer
● Subscription model service
as part of our Firewall/UTM solutions, we also offer network protection against spam as well as viruses, which are often capable of encrypting all company data.
The solution works on the principle of a virtual UTM, which is implemented on the ITH infrastructure side.All company traffic is analysed by the UTM device, which also filters e-mail for spam and viruses. Messages delivered to users are now fully secure.


